LATTICEFIELD.
A quantum-inspired key exchange protocol that replaces algebraic trap-doors with the irreversibility of 30,000-dimensional chaotic attractors. Immune to Shor's Algorithm.
Physics over algebra.
Every key exchange protocol we use today relies on mathematical hardness assumptions. Shor's Algorithm breaks them all.
Every key exchange protocol we use today — Diffie-Hellman, RSA, ECDH — relies on mathematical hardness assumptions. Factoring large primes. Computing discrete logarithms. These are computationally hard for classical computers, but Shor's Algorithm on a quantum computer breaks them all in polynomial time.
I wanted to build a key exchange protocol that doesn't rely on algebraic trap-doors at all. Instead of number theory, the security comes from physics — specifically, the irreversibility of high-dimensional chaotic systems. There's no prime to factor, no discrete log to compute, and no structure for a quantum algorithm to exploit.
The result is a protocol where two parties synchronize their own 30,000-dimensional chaotic attractors over an open channel, and the shared secret is the synchronized state itself — derived, never transmitted.
The Attractor.
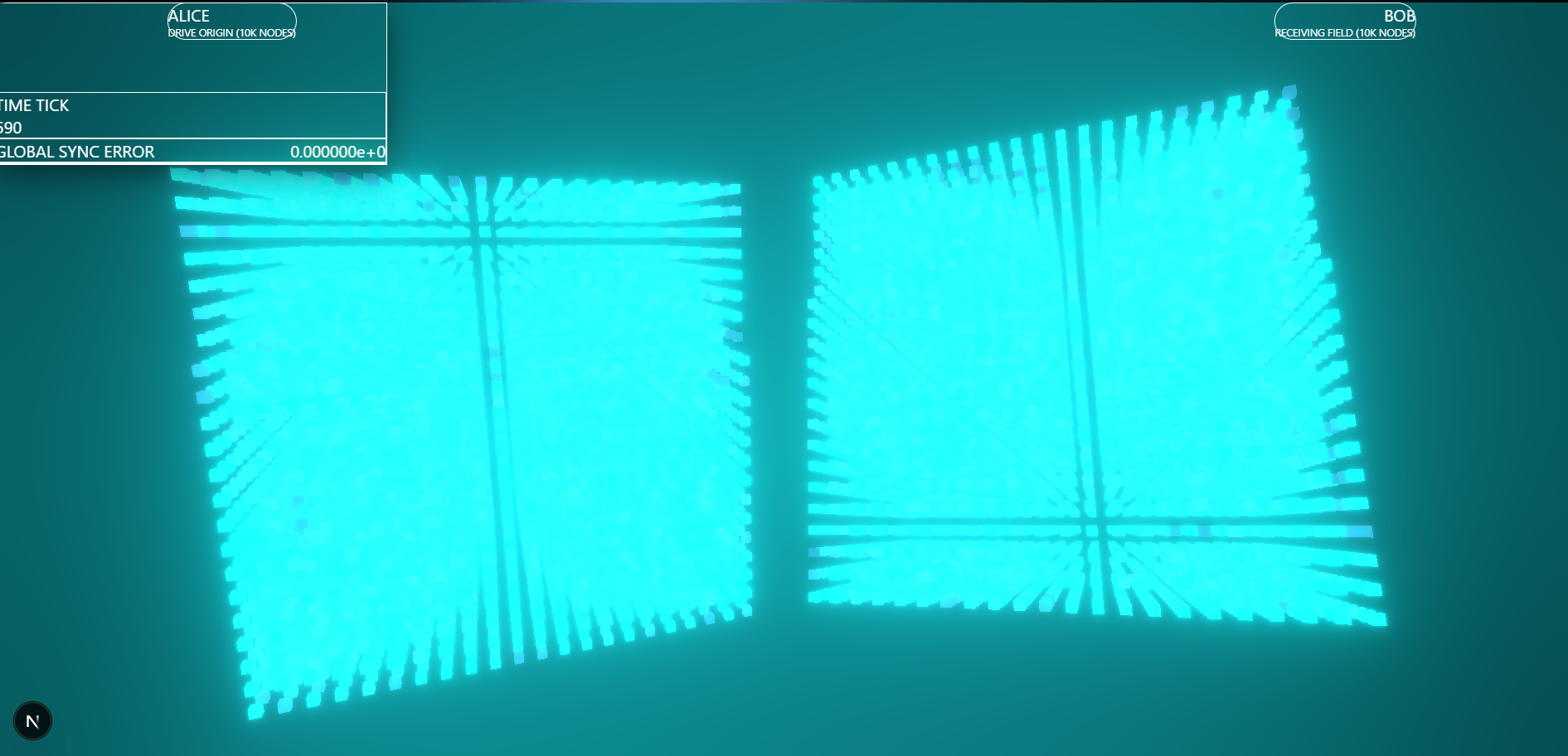
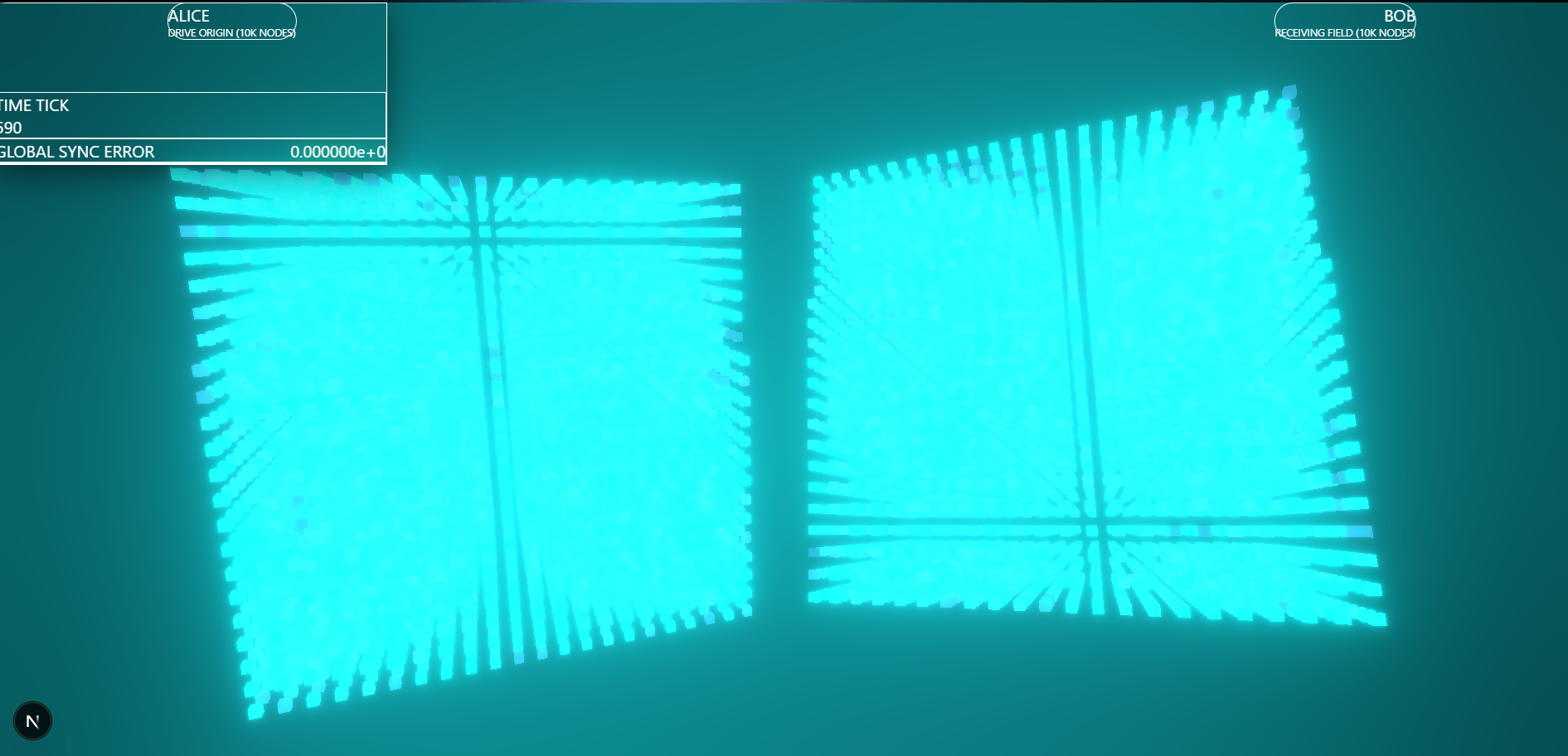
3D representation of the coupled quantum chaotic lattice field. Every point is a node evolving through a 30,000-dimensional phase space.
How it works.
Six layers — from chaotic physics to cryptographic verification.
3D Coupled Chaotic Oscillators
Each of the 10,000 nodes tracks a 3-dimensional quantum probability vector (qx, qy, qz) evolving via three mutually coupled logistic maps. The cross-coupling parameter β makes the system non-separable — you cannot solve any dimension independently. R=4.0 puts every oscillator deep into the chaotic regime.
Coupled Map Lattice (CML)
After each oscillator computes its next state, the Kaneko CML diffusion step blends each node with its 6 nearest neighbors (ε=0.35). This propagates chaotic information spatially across the 3D grid — critical for synchronization to work. Without spatial coupling, pinning would only affect the pinned nodes themselves.
Spatial Pinning Control
1,000 evenly-spaced nodes (10% density) act as the pinning network. Each tick, Alice transmits her state at those locations, and Bob overwrites his pinned nodes. The CML coupling then propagates Alice's information into nearby free nodes — creating a competition between chaos and order that chaos loses.
SHA-256 State Masking
Before transmission, Alice hashes her pinned states with SHA-256. Only the 64-character hex digest is sent — reconstructing the 1,000 input floats from the hash requires 2²⁵⁶ brute-force operations. The shared secret is the synchronized state itself — derived, never transmitted.
Quantum Computer Immunity
Shor's Algorithm needs algebraic structures (factoring, discrete logs) — this protocol has none. Grover's Algorithm provides quadratic speedup on search — but there's no search problem here. The 30,000-dimensional attractor has no known structure a quantum algorithm could exploit.
3D WebSocket Visualizer
A Three.js frontend connects to the physics engine via WebSocket and renders both Alice's and Bob's quantum fields as 3D point clouds. You can watch two completely random clouds converge into a single unified attractor in real time as synchronization completes.
Security Analysis.
Every known attack vector has been analyzed. The protocol has no algebraic structure for quantum algorithms to exploit.
Each node evolves via three mutually coupled logistic maps. The cross-coupling (β) makes the system non-separable — no dimensional reduction attack is possible.
After isolated oscillator computation, the Kaneko CML diffusion blends each node with its 6 spatial neighbors:
Convergence Result
At 10% pinning density, the synchronization error drops to exactly 0.0000000000e+0 — below IEEE 754 double-precision floating-point resolution (~10⁻¹⁵) — within approximately 700–900 ticks at 60Hz. That's about 12–15 seconds.
After convergence, both grids execute bit-for-bit identical trajectories permanently, forming a shared secret that was never transmitted over any channel.
Limitations
Classical simulation
Uses the Quantum Logistic Map from open quantum systems theory — not actual quantum hardware or entanglement.
No authentication layer
Does not verify who Alice is. A full deployment needs PKI or public-key auth before synchronization begins.
Session key derivation
The synchronized state is the secret, but extracting a standard AES-256 key from it needs formal specification.
Not peer-reviewed
Security claims are based on theoretical analysis and empirical testing. Formal proofs have not been published.
Post-quantum
first principles.
This project combines chaos theory, coupled dynamical systems, spatial control theory, and cryptographic hashing into a key exchange protocol with no known quantum vulnerability. If you're working on post-quantum security or nonlinear dynamics, let's talk.